Physical Address
304 North Cardinal St.
Dorchester Center, MA 02124
Physical Address
304 North Cardinal St.
Dorchester Center, MA 02124
Technology reporters
 Google
GoogleTwenty-five years of computer programmers
Away to everyone’s everyone Impacts turned out to be minimal,
Today, most of the critical threats are new to the digital digital infrastructure. But this time, we cannot be rational when it will move from the etheth of the fact, while the spectacles of digital technology means that the matter is more complicated.
That’s because it came a quantity computing by many encrimic algorithms that underpin and have a highly cracked world.
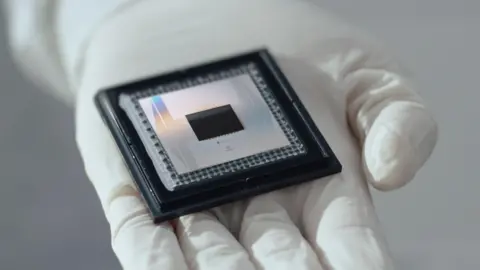
CapThe Capture Damage Botttalkan for “Defeat” used today. Santina processing Birth Bila Bila Bila in one of two countries – one or one or zero, or specific computing using the size, which can be in some countries, or superlakus.
“The reason why it is strong because you do all the possibility at once,” prophanti Sasasgantth, Director of the Sasasgantth, the Sasasgantth Director to the University of Sproy University. This means “more, more efficient, more, stronger.”
This means quantum system offering the possibility of key problems beyond the classic computer, is the region like personvisis as additional medical researchers.
The problem is some similar math problems underpin the encrypted encrypted ionalpoint to ensure confidence, reactions and achievements in the computer network today.
Today’s computer will take Thousands, Even Millions of the current encrypted file, such as RSA. Quantum quantum computer can, theory, do work in minutes.
This has implications for everything in addition to electronic payments and create satellite communications. “Anything is kept by something vulnerable to be a pretty game for people who have access to quantum computer,” French Jon, Pridager isc2.
Computer quantity is capable of breaking the asymmetric encryptes may be in the years
But progress is made.
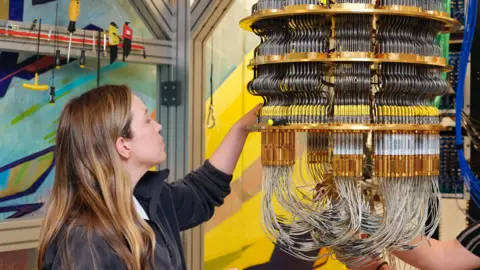
In the month of December, Google speak new quantum chips Submit the key “ripping” and “Chariling Pamping to a quiet computer, another scale”.
Some approximately the quantum device that is capable of breaking the current encryption will require 10,000 times, while others say millions will be required. This day system has several hundred most.
But businesses and governments are strengthening today, as the speaker can harvest an encrypted and decrypting information later when you get a strong idea and device.
 Google
GoogleWet represents, Deputy Designes President Software on strong security and such a device can ask, “Leader in that organization?” Leaders? “
It can be a national security information, personal data, strategic data, strategic plans, and intelligible property and intelligence “in a fast food recipe.
Mrance French Two, if the intermediate composation becomes simple, threats become smaller with transloration that protect our banking transfers, for example, inexactively not broken.
The good news is a research with a technology industry that has been tied a solution to the problem. In August, the National Standard National Institute and National Technology in US is released three quantum’s quantum encryption standards.
This saying will be “reduced electronic information, from the Distribution Email message to the e-commerce transaction that the proper transaction of modern economy.” This encourages a computer system administrator for transition to the standard to the new one as soon as possible, and expressing over 18 algorithms discussed as a backup standard.
 Getty Image
Getty ImageThe problem is meant to be large hammer and all of our technological infrastructure.
“If you think about the number of things outside the existing asynchetry on them, billions of things. We are opening the problem of changes that really,” Mr France Mr France.
Some digital infrastructures will be wound easily to improve. Your browser, for example, will only accept the upgrade from Vendor said MRANCE. “Widina really is right on the discrete device (IOT),” he said.
This may be difficult to track, and cannot be accessed. Some devices – decay device in critical national infrastructure such as water systems, for example – will not be strong enough to handle new encryption standards.
Mr Chacmmore said the industry has arranged the encrypted transition in the past, but “it is a better discinuity that makes this threat.”
So, trying to help the customer build “the possibility of Crypo” by setting policy now and use Automation to identify with the secure assets. “That’s a secret to make this transition relating to not.”
And challenges extend into space. Up Sudprians say many satellites – such as a graping network – should like a straight, even if it means a temporary individual device.
“At the same time, especially with Leo (low orbit earth)), you have 10 to 20 satallite above your head,” profession. “So, if one can serve you, good what? There are nine others who can serve you.”
More challenges, saying, is the “great one and other time, which includes a more traked power. Increases the hardware specific modules means to replace the entire device . However, says girlfriend, this is a matter of plymy that more often and fare launched.
When the impact of the Hase Millennum Bug has been minimal in the first day of 2000, it’s due to a large amount of work has been discussed to be in university at university.
Obviously, he added, that it is not possible, encryption now will be vulnerable.
“With crindography,” Mr depresiar “if someone breaks your system, you just know once you have got your data.”